Wpa2 How To Crack

EDITOR S NOTE: Be advised, in order to perform this exercise, you WILL need to see Offensive Security As Your Self Defense. This will instruct you on how and where to download and install Kali Linux. It is essential that you download the correct version for your machine s archetype. The instructions are simple if you follow them correctly. Leave a comment with any questions.
Also, check out my latest video tutorial Hacking Accounts Using SSLstrip and Arpspoof.
People assume that because their wireless encryption key is WPA2 standard, they are safe from cyber attack. They are wrong. Reaver is a program inside of Kali Linux that allows an attacker maybe that creepy neighbor of yours that never comes out of their apartment without taking weird to a new level, easily compromise your routers password by attacking the PIN authorization process between your router and other devices. See, with your router s PIN, a password is not needed. In fact, because Reaver doesn t use a dictionary file to bruteforce your password, it doesn t matter how strong or long it is and Reaver WILL eventually crack the PIN.
Your router s PIN is eight 8 numbers long. Your router knows four of these numbers and any devices that use the wireless password knows the other four numbers. Reaver randomly runs every possible combination of four numbers until it cracks the PIN. Then voila. The attacker gets your full PIN and your Password..
How to protect yourself:
Set your wireless router to LOCK WPS. This locks your WPS PIN and makes you invulnerable to this method of attack.
Lets Learn How This Attack Is Carried Out
In order to use Reaver, you need to get your wireless card s interface name, the BSSID of the router you re attempting to crack which I will show you how to find, and you need to make sure your wireless card is in monitor mode. So let s do all that.
Find your wireless card:
Inside Terminal, type: iwconfig
Press Enter. You should see a wireless device in the subsequent list. Most likely, it ll be named:
wlan0 or wlan1
But if you have more than one wireless card, or a more unusual networking setup, it may be named something different.
Put your wireless card into monitor mode: Assuming your wireless card s interface name is: wlan0
Execute the following command to put your wireless card into monitor mode:
airmon-ng start wlan0
This command will output the name of monitor mode interface, which you ll also want to make note of. Most likely, it ll be: mon0
Find the BSSID of the router you want to crack:
Lastly, you need to get the unique identifier of the router you re attempting to crack so that you can point Reaver in the right direction. To do this, execute the following command:
airodump-ng mon0
When you see the network you want, press Ctrl C to stop the list from refreshing, then copy that network s BSSID it s the series of letters, numbers, and colons on the far left. The network should have WPA or WPA2 listed under the ENC column.
Now, with the BSSID and monitor interface name in hand, you ve got everything you need to start up Reaver.
Crack a Network s WPA Password with Reaver
To find out if the AP you are attacking usese WPS vulnerable to Reaver, you can use:
wash -i mon0
Look under the LOCK column. If your target BSSID has it s WPS LOCKED you will see yes for LOCKED WPSs, then Reaver will not be able to crack the PIN. If you see a no, then continue
Now execute the following command in the Terminal. replacing and monitor interface and the BSSID with the BSSID that you copied down above :
reaver -i mon0 -b bssid -vv
For example, if your monitor interface was mon0 like mine, and your BSSID was
8D:AE:9D:65:1F:B2
a BSSID I just made up, your command would look like:
reaver -i mon0 -b 8D:AE:9D:65:1F:B2 -vv
Press Enter, sit back, and let Reaver work its disturbing magic. Reaver will now try a series of PINs on the router in a brute force attack, one after another. This will take a while. In my successful test, Reaver took about 6 hours to crack the PIN and deliver me the correct password. The Reaver documentation says it can take between 4 and 10 hours so it could take more or less time than I experienced, depending.
THIS TUTORIAL IS INTENDED FOR INFORMATIONAL AND EDUCATIONAL USE ONLY
Use these techniques only on networks that you explicitly own.
Like this:
Like Loading
Related.

How to Hack Wi-Fi: Cracking WPA2-PSK Passwords Using Aircrack-Ng. Welcome back, my greenhorn hackers. When Wi-Fi was first developed in the late 1990s, Wired.
Today I am going to teach you how to easily hack WPA/WPA2-PSK enabled network using reaver. But, for that the targeted router should support WPS WiFi Protected Setup which is supported by most of the router nowadays. WPS is an optional device configuration protocol for wireless access points which make it really easier to connect.
This feature exist in most of the router for the easy setup process through the WPS pin which is hard-coded into the wireless access point. Reaver takes the advantage of a vulnerability in WPS. Thanks to Craig Heffner for releasing an open-source version of this tool named Reaver that exploits the vulnerability. In simple tone, Reaver tries to bruteforce the pin; which in result reveal WPA or WPA2 password after enough time.
What You ll Need
You do not have to be a expert at Linux or in even using computer. The simple command-line console will do all the things. But you may need a lot of time for this process and also some luck. The brute force may take from 2 hours to more than 10 hours too sometimes. There are various ways to set up reaver but here are the requirement for this guide.
Backtrack OS. Backtrack is a bootable Linux distribution with lots of pen-testing tools. You can use various other Linux distribution but I prefer backtrack. If you don t know how to install backtrack then please check this link first.
A computer and wireless network card. I cannot guarantee if this will work with all the internal wireless card but i recommend a external wireless card.
A lot of Patience. The process is simple but brute forcing the PIN takes a lot of time. So you have to be patience. Kicking the Computer won t help you this time.
Let s Get Started
Now you should have a backtrack OS ready for action.
Step 1: Boot into BackTrack
You can use any method to boot into backtrack; like from live cd, VMware, dual boot, etc. So, just boot it first into the GUI mode and open up a new console command line which is in the taskbar. So just boot into backtrack. During the boot process, BackTrack will prompt you to to choose the boot options. Select BackTrack Text – Default Boot Text Mode and press Enter.
After some time Backtrack will take you into a command line prompt where you should type startx and press Enter. BackTrack will boot will into Graphical User Interface GUI mode.
Step 2: Install Reaver Skip this step if you are using BackTrack 5
Reaver should be already installed in the Backtrack 5 but if you are using older backtrack or any other Linux distribution you can install Reaver by using few steps below.
First Connect your BackTrack to the internet. For WiFi connection go to Application Internet Wicd Network Manager
Select your network and click connect and input your password if necessary, click OK and click CONNECT the second time.
Now that you are connected to internet its time to install Reaver. Click the terminal icon in the menu bar. And at the console type the following:
apt-get update
apt-get install reaver
Now if everything worked fine you will get a freshly installed Reaver tool. Now if you are testing it in your own system then please go to Wicd Network Manager and Disconnect yourself first.
Step 3 : Gather Information
Before launching the Reaver attack you need to know your target wireless network name, BSSID it is the series of unique letters and number of a particular router and its channel number. So to know this make your wireless card into monitor mode and gather the required information of the access points. So let us do all these things.
First lets find your wireless card. Inside terminal or console, type:
airmon-ng
Press Enter and there you should see a list of interface names of different devices. There should be a wireless device in that list you you have connected it to BackTrack. Probably it may be wlan0 or wlan1.
Note: To connect your wireless network card into WMware. Firstly, connect it to the USB and then you will see a small USB icon like in the figure in the top right of VMware. Then, right click on it and click connect. At last, USB sign will turn into green colour and start to glow.
Enable monitor mode. Supposing your wireless card interface name as wlan0, type this command in that same console.
airmon-ng start wlan0
This code will create a new monitor mode interface mon0 like in the screenshot below which you want to keep note of.
Search the BSSID of the Access Point router you want to crack. There are few ways to search for the Access Point BSSID but I prefer to use the inbuilt reaver search method which shows the list of WPS vulnerable BSSID only.
In the console type this following command and press enter:
wash -i mon0
You will see the list of wireless networks that support WPS which are vulnerable to Reaver as seen in the screenshot below. After few minutes you can stop the scan by pressing Ctrl C.
Step 4: Lets start Cracking
I suggest you to try to crack the ones which have WPS lock disabled or say NO in WPS Locked column. It may also work if it says YES but I am not sure of that. For that, copy the BSSID of the target AP and also keep note of its channel and in the console and type the following and Enter:
reaver -i monitormode -c channel -b targetbssid -vv
For My Case the monitor mode will be mon0 channel would be 1, targetbssid would be C8:3A:: and -vv is written to show the current statistic of the attack like percentage completed, currently brute forcing PIN and so on; so we will type the following and enter:
reaver -i mon0 -c 1 -b C8:3A:: -vv
Press Enter and if everything goes right then you will see the attack process like in the screenshot below. Please note that you will not get Restore previous session like me because I have already tried to crack it so, it is prompting me to either to resume from that paused point or not. Your progress will also be saved if your press Ctrl C. It will prompt you the same if you again hit the same above command and you can resume it from there.
Now just wait or have some coffee and let Reaver do its magic. It might take from 2 hours to 10 hours or more. There are 8 numeric digits of WPS but due the fact that WPS authentication protocol cuts the pin in half and validates each half separately. Since the last digit of pin is a cheksum value which can be calculated on the basis of previous value there are 10 4 10,000 possible values for first half and then 10 3 1000 values for the last pin. So the WPS pin code can be calculated in 11,000 possible pin code. Some AP can check the WPS pin in the rate of 1 pin per second and some take more so the time depend upon the AP and even the network connection strength depends too.
When the PIN is successfully brute-forced Reaver will show you the WPS PIN and the plain password of the AP like in the below screenshot.
I recommend you to keep note of the WPS pin so that if the password is changed again you can hack that in few seconds the next time by using the following process.
reaver -i monitor interface -b BSSID -c channel --pin 8 digit pin -vv
Example:
reaver -i mon0 -b :: -c 1 --pin 12345678 -vv
So now the error part as you might get a bunch of error depending upon your conditions. You might get some timeout but it is normal but if you are getting other errors then see the below Error section for that
Error Section:
If you are getting the following error then check the corresponding solution for that.
If 10 consecutive unexpected WPS errors are encountered, a warning message will be shown. Since this may be a sign that the AP is rate limiting pin attempts, a waiting command can be issued that will occur whenever these warning messages appears by issuing the following command:
reaver -i mon0 -b :: --fail-wait 360
The default receive timeout period is 5 seconds. This timeout period can be set manually if necessary minimum timeout period is 1 second :
reaver -i mon0 -b :: -t 3
The default delay period between pin attempts is 1 second. This value can be increased or decreased to any value. Please note that 0 means no delay:
reaver -i mon0 -b :: -d 0
So here ends the tutorial on how to crack wireless network easily using reaver. Good Luck Hacking
Related.
We have updated our tutorial on how to crack WPA / WPA2 with even more powerful and easier to use passphrase recovery tools. We ve also added tips for creati.
Aug 27, 2013 - WPA2 uses a stronger encryption algorithm, AES, that s very difficult to crack but not impossible. My beginner s Wi-Fi hacking guide also Getting Started with Terms - Cracking WPA2-PSK - Dictionary Attack5 Steps Wifi Hacking – Cracking WPA2 Password Ethical www.hacking-tutorial.com Hacking TutorialCachedSimilarToday we will learn about 5 Steps Wifi Hacking - Cracking WPA2 Password. A lot of readers send many request regarding how to crack wireless WPA2.

Hacking WPA / WPA2 Encrypted NetworksPart II of my Network Security How-To Series: 1 ARP Spoofing from a Mobile Device 2 Hacking WPA / WPA2 Encrypted.

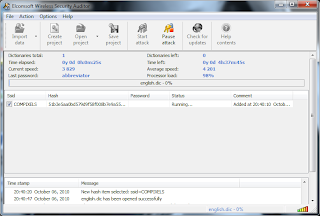
- Dec 26, 2013 1. CommView for Wifi - 2. Elcomsoft Wireless Security Auditor - Visit our blog.
- Aug 13, 2015 This feature is not available right now. Please try again later. Published on Aug 13, 2015. Category. Science Technology; License. Standard YouTube License.
- Thank you now I can protect myself from this type of attack. FYI there is specialized firmware that you can put on your router/modem that will give you more security.